Okta integration guide
In this tutorial you will learn how to connect your Area 1 account to Okta. When single sign-on (SSO) is correctly configured, your authorized employees can connect to the Area 1 dashboard using a familiar user name and password.
1. Create an Area 1 app in Okta
You will need to manually create an app for Area 1 in Okta.
-
Log in to Okta as an administrator.
-
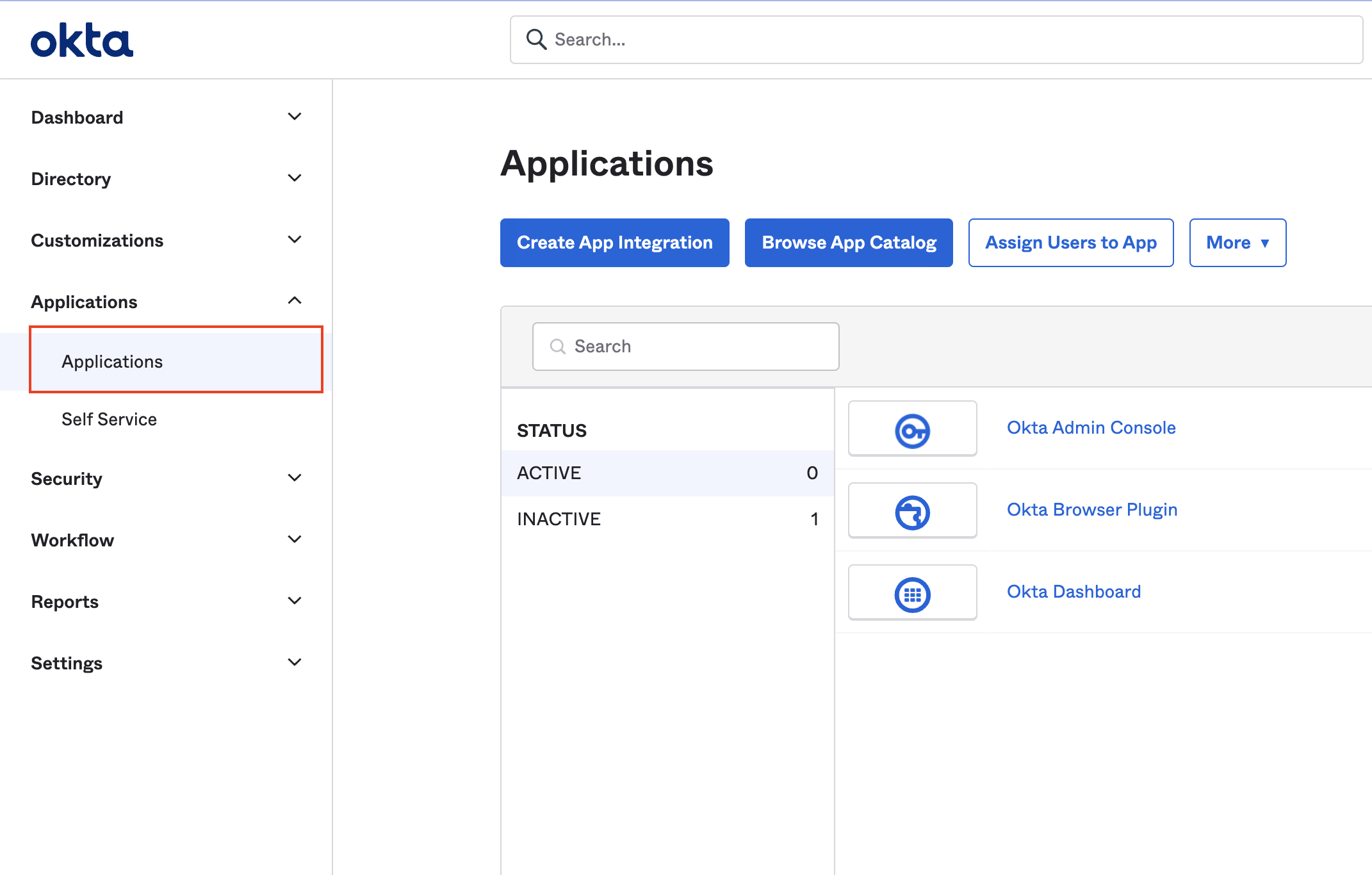
In the Admin console, go to Applications > Applications.
-
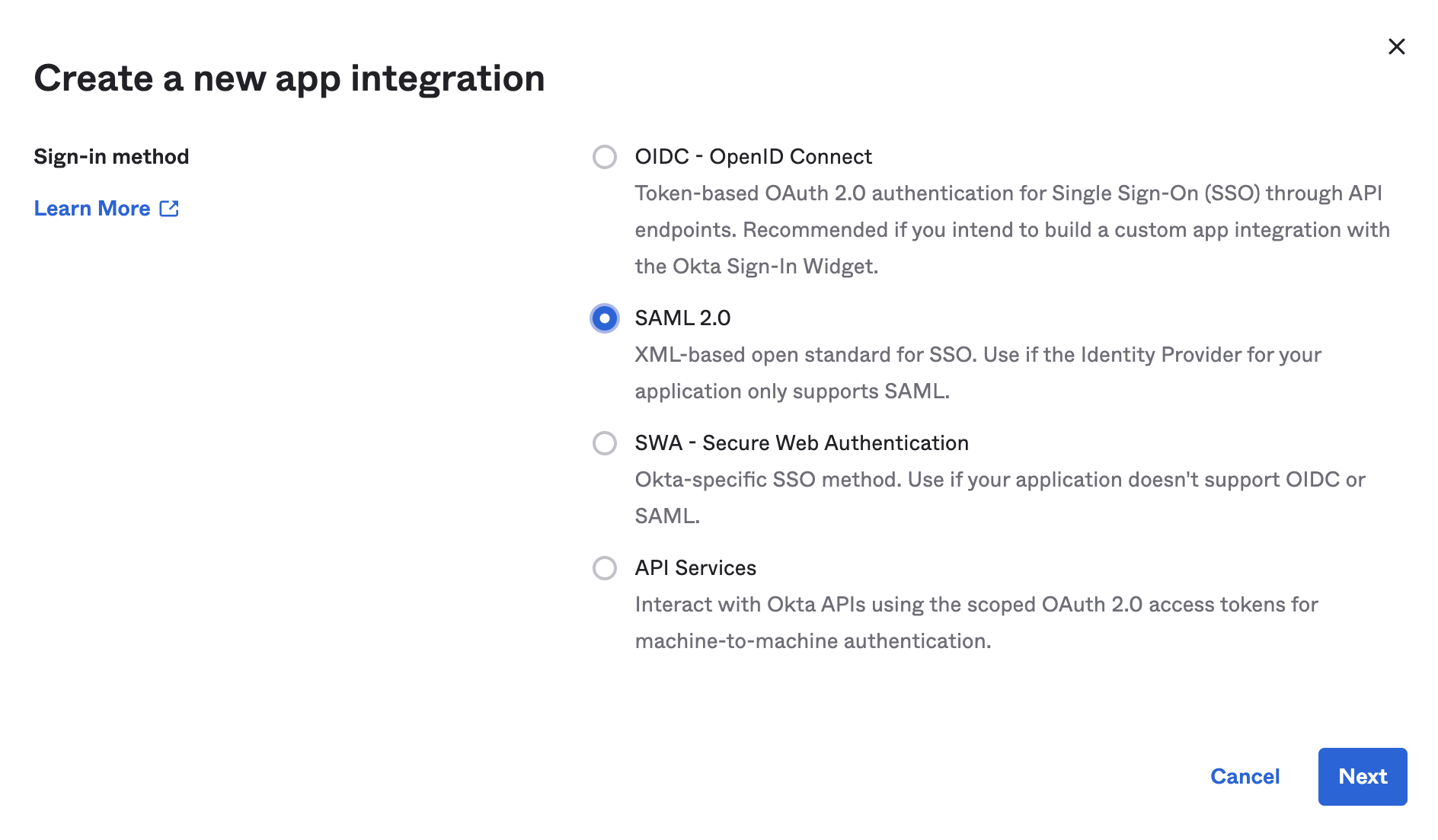
Select Create App Integration > SAML 2.0, and select Next.
-
Enter a descriptive name for your app, such as
Area 1, and select Next. -
Enter the following settings for SAML Settings:
Single sing on URL https://horizon.area1security.com/api/users/samlAudience URI (SP Entity ID) https://horizon.area1security.com/api/users/samlName ID format Select EmailAddress from the drop-down menu. Application username Select Email from the drop-down menu. Response Signed Assertion signature Unsigned Signature Algorithm RSA-SHA1 Digest Algorithm SHA1 Attribute statements (optional) Name Enter email addresses for your users. Should match users already added to Area 1 dashboard. Name format Select Unspecified from the drop-down menu. Value Select user.emailfrom the drop-down menu.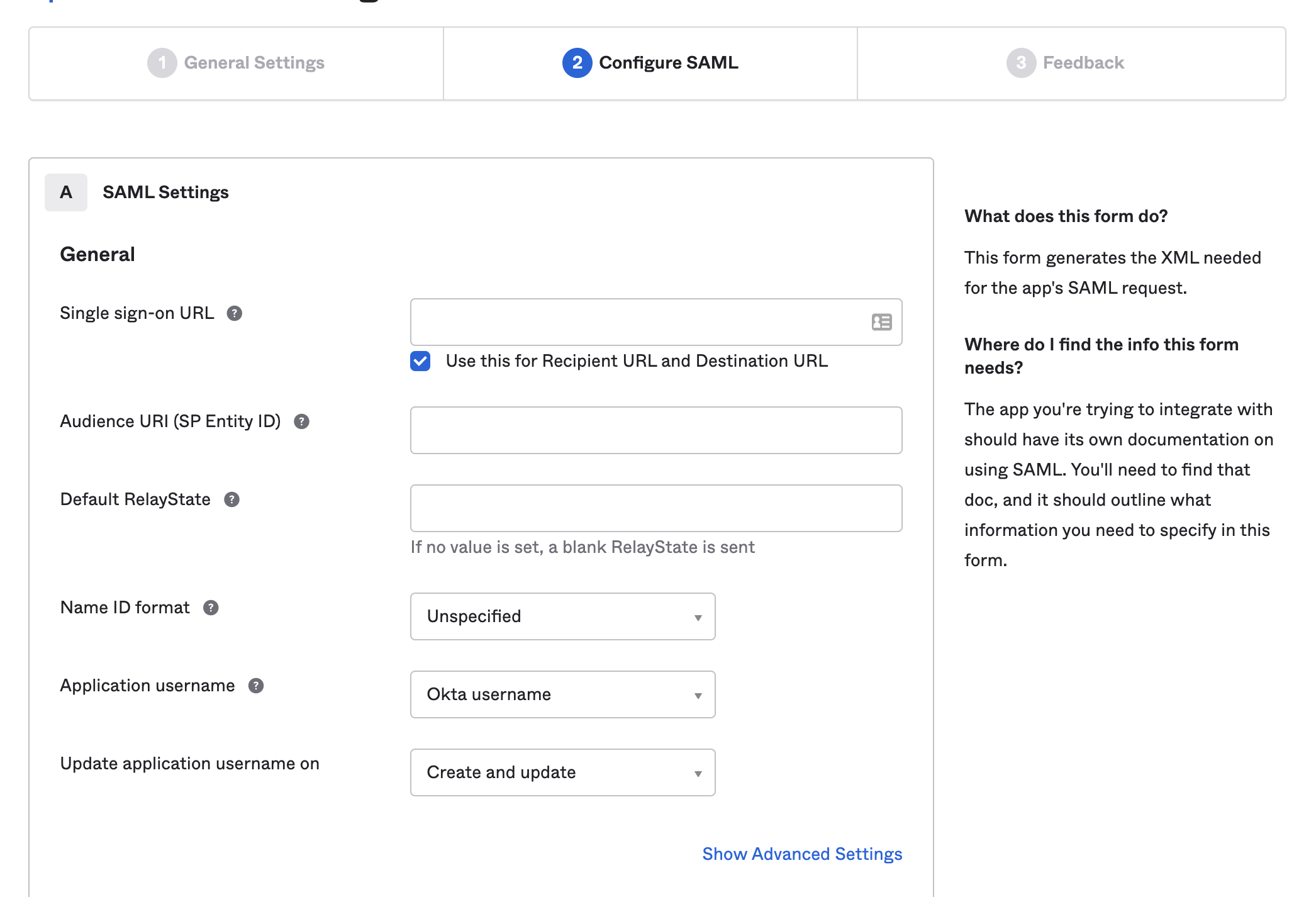
-
Select Next.
-
Under Are you a customer or a partner?, select I’m an Okta customer adding an internal app.
-
In App type, select This is an internal app that we have created.
-
Select Finish.
-
Okta should display the app you have just created. If not, go to Applications > Applications, and select it.
-
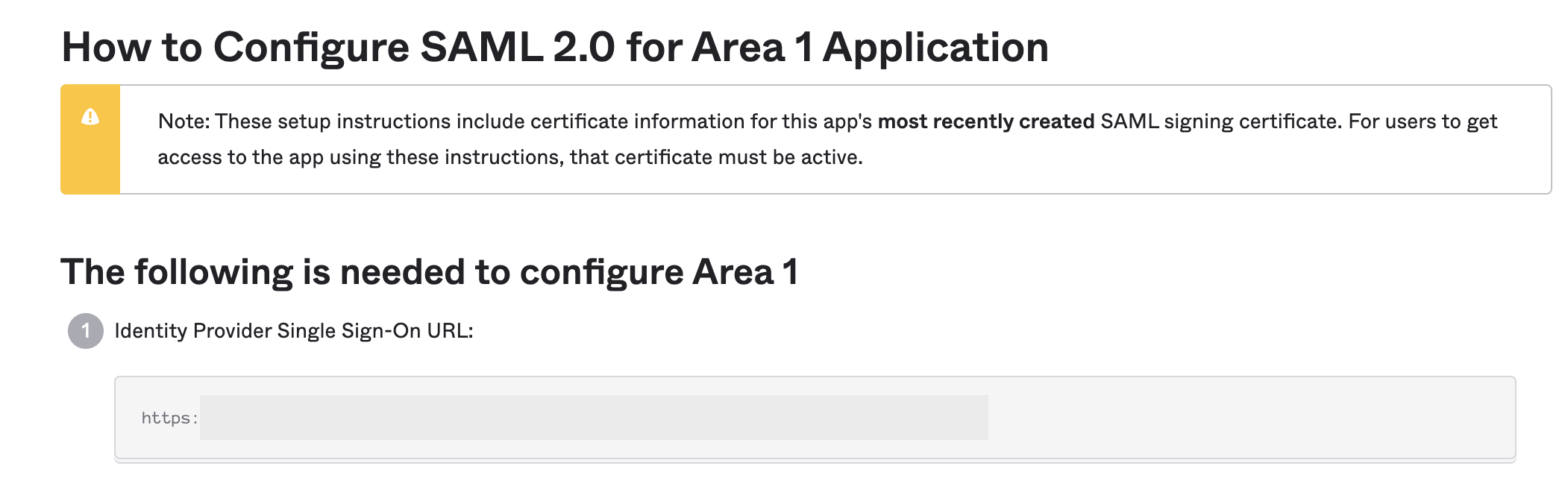
In the Sign On tab, go to View SAML setup instructions and select it to retrieve the SAML provider information.
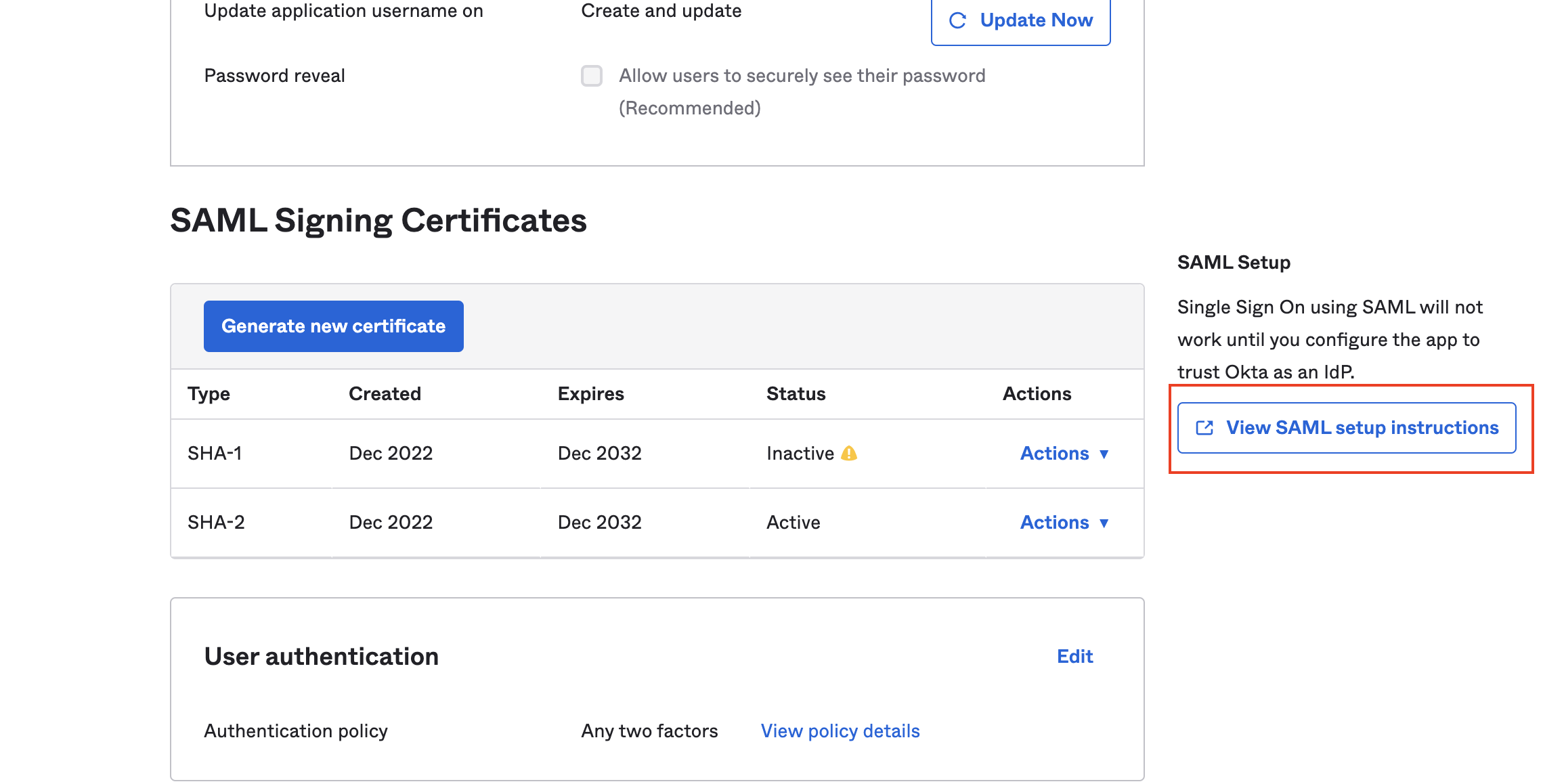
-
Copy and save the link in Identity Provider Single Sign-On URL. You will need it later to use in the Area 1 dashboard.
-
Scroll down to Optional. You might need to enlarge the text box to copy and save all the XML data. You will need this information to finish configuration in the Area 1 dashboard. The start of the metadata should be similar to the following:
<?xml version="1.0" encoding="utf-8"?><EntityDescriptor ID="_<YOUR_DESCRIPTIOR_ID>" entityID="https://<YOUR_ENTITY_ID> " xmlns="urn:oasis:names:tc:SAML:2.0:metadata">...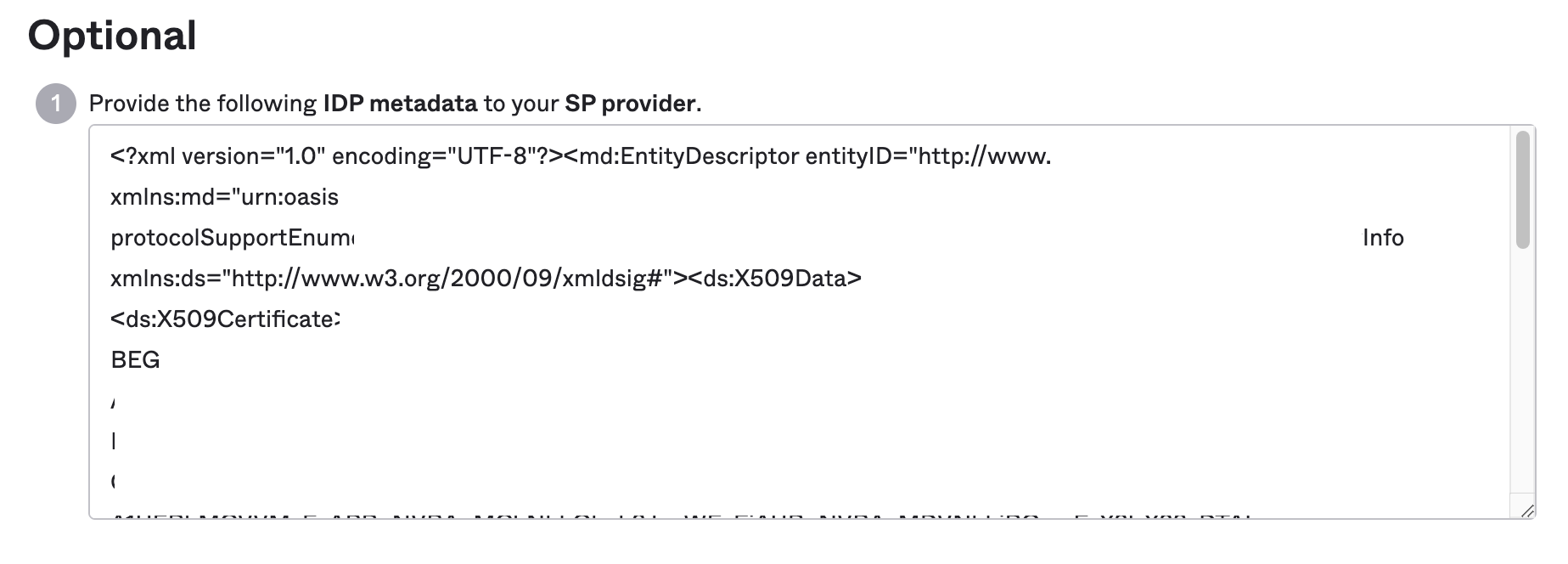
2. Configure Area 1 to connect to Okta
-
Log in to the Area 1 dashboard.
-
Go to Settings (the gear icon).
-
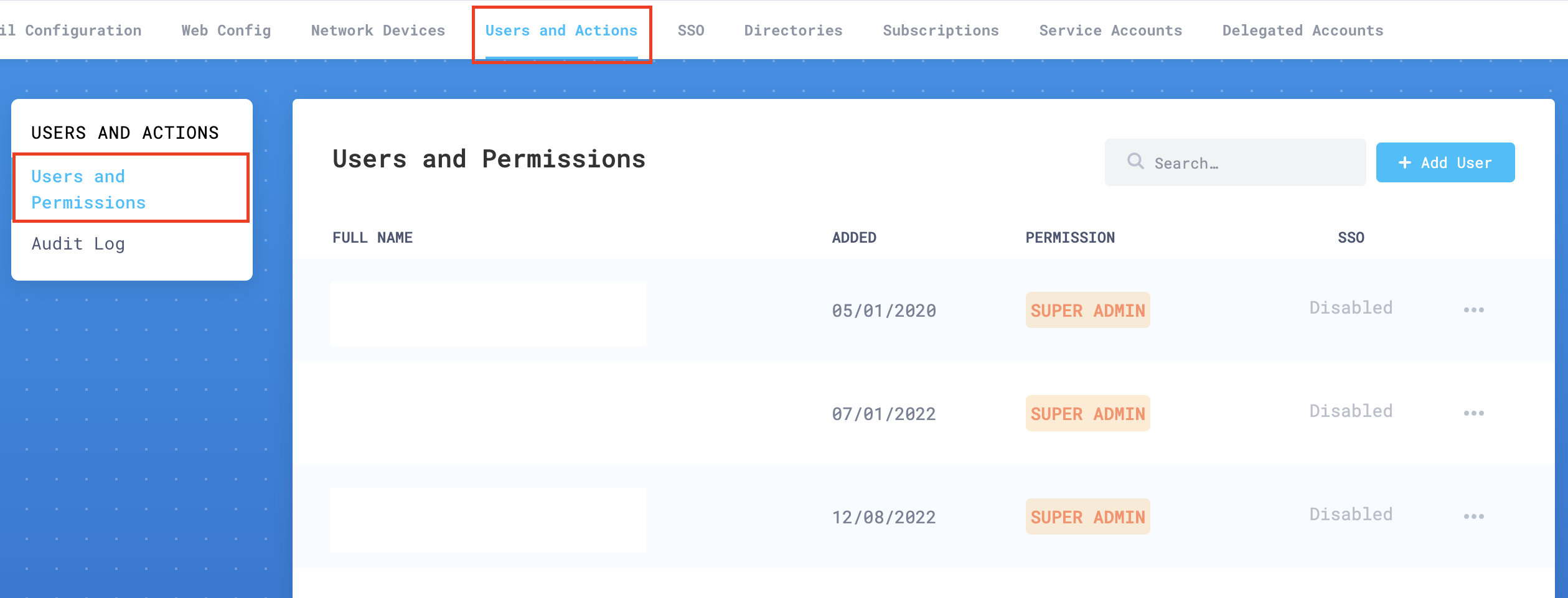
In Users and Actions > Users and Permissions add the email addresses of all your authorized administrators.
-
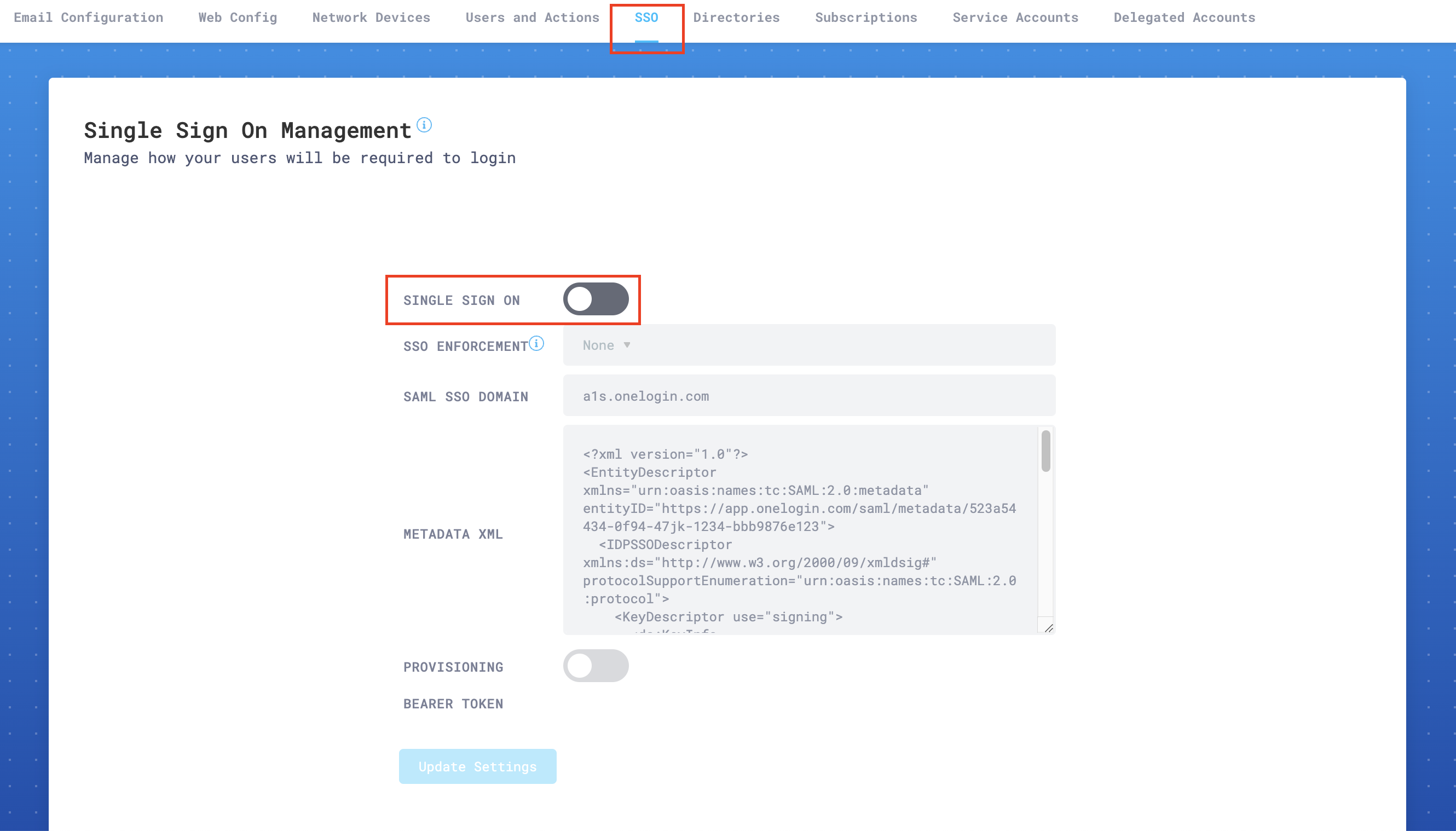
Go to SSO Settings and enable Single Sign On switch.
-
In SSO Enforcement, choose one of the settings according to your specific needs:
- None: This setting allows each user to choose SSO, or username and password plus 2FA (this is the recommended setting while testing SSO).
- Admin: This setting will force only the administrator account to use SSO. The user that enables this setting will still be able to log in using username and password plus 2FA. This is a backup, so that your organization does not get locked out of the portal in emergencies.
- Non-Admin Only: This option will require that all
Read onlyandRead & Writeusers use SSO to access the portal. Admins will still have the option to use either SSO or username and password plus 2FA.
-
In SAML SSO Domain enter the domain you saved from step 13. For example,
area1security-examplecorp.okta.com. -
In Metadata XML paste the XML metadata you saved from step 14.
-
Select Update Settings to save your configuration.
Log out of any customer portal sessions. Your Okta account should now show a tile for Area 1.