Enable Gateway proxy with PAC files
You can apply Gateway HTTP policies at the browser level by configuring a Proxy Auto-Configuration (PAC) file. The PAC file contains a JavaScript function which instructs a browser to forward traffic to a proxy server instead of directly to the destination server. When end users visit a website, their browser will send the request to a Cloudflare proxy server associated with your account to be filtered by Gateway.
Prerequisites
Install the Cloudflare certificate on your device.
1. Generate a proxy endpoint
You can generate a proxy endpoint on the Zero Trust dashboard or through the Cloudflare API.
Create a proxy endpoint (dashboard)
- In Zero Trust, go to Gateway > Proxy Endpoints.
- Select Create endpoint.
- Give your endpoint any name.
- Enter the public source IP address of your device(s) in CIDR notation. For example,
- IPv4:
90.90.241.229/32(up to/26) - IPv6:
2601:645:4500:9c0:a945:f47c:23e9:a35b/128
- IPv4:
- Select Save endpoint and confirm the endpoint creation.
Your Cloudflare proxy server domain is of the form:
Create a proxy endpoint (API)
-
Run the following command:
curl --request POST \--url https://api.cloudflare.com/client/v4/accounts/<ACCOUNT_ID>/gateway/proxy_endpoints \--header 'X-Auth-Email: <EMAIL>' \--header 'X-Auth-Key: <API_KEY>' \--data '{"name": "any_name", "ips": ["<PUBLIC_IP>", "<PUBLIC_IP2>", "<PUBLIC_IP3>"]}'Replace
<PUBLIC_IP>with the source IP address of your device in CIDR notation. For example,- IPv4:
90.90.241.229/32(up to ‘/25’) - IPv6:
2601:645:4500:9c0:a945:f47c:23e9:a35b/128(up to ‘/109’)
After running the command, you should see an output similar to
{"result": {"id": "d969d7bf-ec28-4291-9af0-86825f472c21","name": "test","created_at": "2022-03-02T10:57:18.094789Z","updated_at": "2022-03-02T10:57:18.094789Z","ips": ["90.90.241.229/32"],"subdomain": "3ele0ss56t"},"success": true,"errors": [],"messages": []} - IPv4:
-
Note the
subdomainvalue returned by the API. Your Cloudflare proxy server domain is of the form:<SUBDOMAIN>.proxy.cloudflare-gateway.comIn the example above, the subdomain is
3ele0ss56tand the proxy server domain is3ele0ss56t.proxy.cloudflare-gateway.com.
2. Test your proxy server
-
In Zero Trust, create an HTTP policy for testing purposes. For example:
Selector Operator Value Action Domain in example.comBlock -
Verify that nothing is returned by a
curlcommand:$ curl -4 -p -x https://3ele0ss56t.proxy.cloudflare-gateway.com https://example.com
3. Create a PAC file
A PAC file is a text file that specifies which traffic should redirect to the proxy server.
Below is the default PAC file. You can customize the file and host it somewhere your browser can access, such as on an internal web server or on Cloudflare Workers.
4. Configure your browser
All major browsers support PAC files. You can configure individual browsers, or you can configure system settings that apply to all browsers on the device. Multiple devices can call the same PAC file as long as their source IP addresses were included in the proxy endpoint configuration.
The following example demonstrates the setup procedure for Firefox.
-
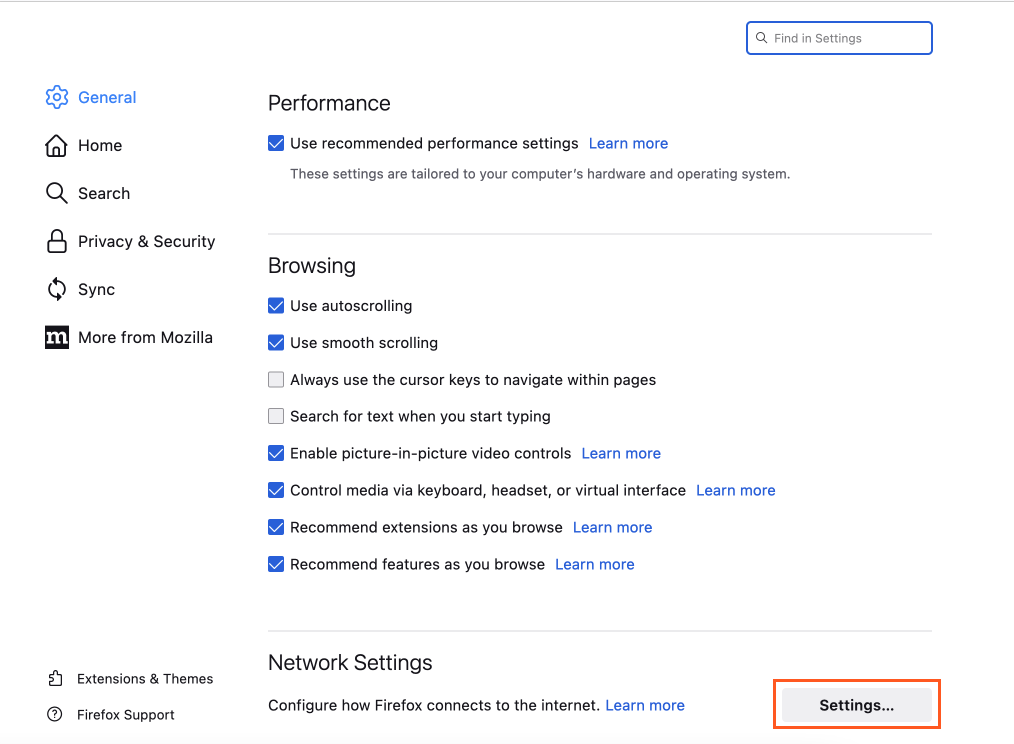
In Firefox, go to Settings and scroll down to Network Settings.
-
Select Settings.
-
Select Automatic proxy configuration URL.
-
Enter the URL where your PAC file is hosted, for example
https://proxy-pac.cflr.workers.dev/3ele0ss56t.pac.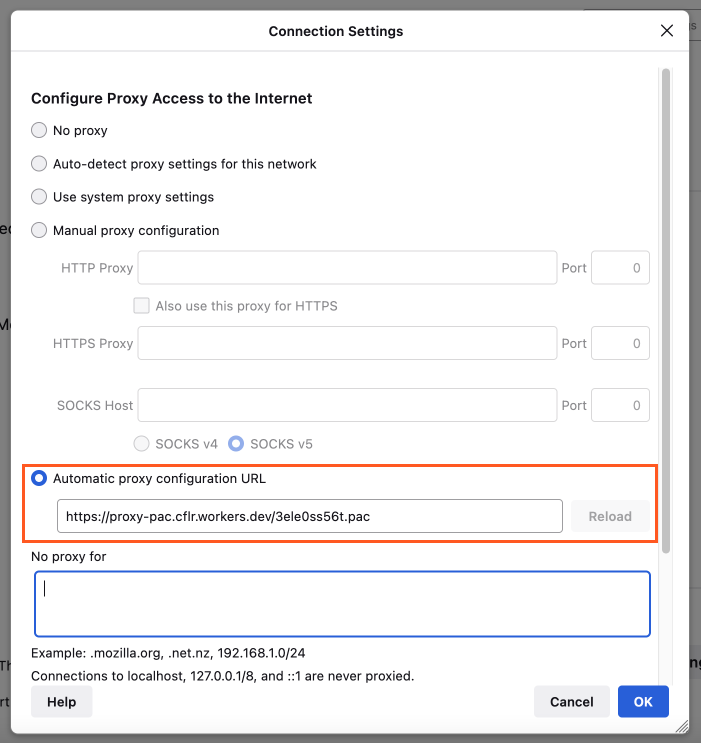
-
Select OK. HTTP traffic from Firefox is now being filtered by Gateway.
5. Test your HTTP policy
You can test any supported HTTP policy, such as the example policy created in Step 2. When you go to https://example.com in your browser, you should see the Gateway block page.
Limitations
At this time, the agentless HTTP proxy does not support identity-based policies, mTLS authentication, or UDP traffic. To enforce HTTP policies for UDP traffic, you must disable QUIC in your users’ browsers.