Install the Cloudflare certificate
If your device does not support certificate installation via WARP, you can manually install the Cloudflare certificate. You will need to add the certificate to both the system keychain and to individual application stores. These steps will need to be performed on each new device that is to be subject to HTTP filtering.
Download the Cloudflare root certificate
First, download the Cloudflare certificate. The certificate is available both as a .pem and as a .crt file. Certain applications require the certificate to be in a specific file type, so ensure you download the most appropriate file for your use case.
Verify the certificate fingerprint
To verify your download, check that the certificate’s thumbprint matches:
SHA1
➜ ~ openssl x509 -noout -fingerprint -sha1 -inform der -in <Cloudflare_CA.crt>
SHA1 Fingerprint=BB:2D:B6:3D:6B:DE:DA:06:4E:CA:CB:40:F6:F2:61:40:B7:10:F0:6C
➜ ~ openssl x509 -noout -fingerprint -sha1 -inform pem -in <Cloudflare_CA.pem>
SHA1 Fingerprint=BB:2D:B6:3D:6B:DE:DA:06:4E:CA:CB:40:F6:F2:61:40:B7:10:F0:6C
SHA256
➜ ~ openssl x509 -noout -fingerprint -sha256 -inform der -in <Cloudflare_CA.crt>
sha256 Fingerprint=F5:E1:56:C4:89:78:77:AD:79:3A:1E:83:FA:77:83:F1:9C:B0:C6:1B:58:2C:2F:50:11:B3:37:72:7C:62:3D:EF
➜ ~ openssl x509 -noout -fingerprint -sha256 -inform pem -in <Cloudflare_CA.pem>
sha256 Fingerprint=F5:E1:56:C4:89:78:77:AD:79:3A:1E:83:FA:77:83:F1:9C:B0:C6:1B:58:2C:2F:50:11:B3:37:72:7C:62:3D:EF
Add the certificate to operating systems
macOS
To install the Cloudflare certificate in macOS, you can use either the Keychain Access application or a terminal. Both methods require you to download the Cloudflare certificate in .crt format.
Keychain Access
In Keychain Access, you can choose the keychain in which you want to install the certificate. Each keychain impacts which users will be affected by trusting the root certificate.
| Keychain | Access scope |
|---|---|
| login | The logged in user |
| Local Items | Users with access to cached iCloud passwords |
| System | All users on the system |
To install the certificate with Keychain Access:
-
Download the Cloudflare certificate.
-
Open the
.crtfile in Keychain Access. If prompted, enter your local password. -
In Keychain, choose the access option that suits your needs and select Add.
-
In the list of certificates, locate the newly installed certificate. Keychain Access will mark this certificate as not trusted. Right-click the certificate and select Get Info.
-
Select Trust. Under When using this certificate, select Always Trust.
The root certificate is now installed and ready to be used.
Terminal
The following procedure will install the Cloudflare certificate to your keychain via the command line.
- Download the Cloudflare certificate.
- Open Terminal.
- Add the certificate to your keychain:
This keychain will allow all users on the system access to the certificate. If you want to install the certificate to a different keychain, replace System.keychain with the name of that keychain. For information on the scope of each keychain, refer to Keychain Access.
- Update the OpenSSL CA Store to include the Cloudflare certificate:
Windows
Windows offers two locations to install the certificate, each impacting which users will be affected by trusting the root certificate.
| Store location | Access scope |
|---|---|
| Current User Store | The logged in user |
| Local Machine Store | All users on the system |
-
Right-click the certificate file.
-
Select Open. If you see a Security Warning, choose Open to proceed.
-
The Certificate window will appear. Select Install Certificate.
-
Now choose a Store Location. If you see a security warning, choose Yes to proceed.
-
On the next screen, select Browse.
-
In the list, choose the Trusted Root Certification Authorities store.
-
Select OK, then select Finish.
The root certificate is now installed and ready to be used.
Linux
The location where the root certificate should be installed is different depending on your Linux distribution. Follow the specific instructions for your distribution.
Debian-based distributions
The following procedure applies to Debian-based systems, such as Debian, Ubuntu, and Kali Linux.
- Download the
.pemcertificate. - Copy the certificate to the system, changing the file extension to
.crt.
- Import the certificate.
Red Hat-based distributions
The following procedure applies to Red Hat-based systems, such as Red Hat Enterprise Linux (RHEL), Fedora, Rocky Linux, and AlmaLinux.
- Download both the
.crtcertificate and the.pemcertificate. - Copy both certificates to the trust store.
- Import the certificate.
NixOS
NixOS does not use the system certificate store for self updating and instead relies on the certificates found in ~/.nix-profile/etc/ssl/certs or provided by NIX_SSL_CERT_FILE at runtime.
iOS
iOS only allows the Safari browser to open and install certificates.
-
Open Safari and download the Cloudflare certificate. The device will show a message: This website is trying to download a configuration profile. Do you want to allow this?
-
Select Allow.
-
Go to Settings, where a new Profile Downloaded section will appear directly beneath your iCloud user account info.
-
Select Install. If the iOS device is passcode-protected, you will be prompted to enter the passcode.
-
Next, a certificate warning will appear. Select Install. If a second prompt appears, select Install again.
-
Next, the Profile Installed screen will appear. Select Done. The certificate is now installed. However, before it can be used, it must be trusted by the device.
-
Go to Settings > General > About > Certificate Trust Settings. The installed root certificates will be displayed under Enable full trust for root certificates.
-
Enable the Cloudflare certificate.
-
A security warning message will appear. Choose Continue.
The root certificate is now installed and ready to be used.
Android
-
Go to Settings > Security > Advanced > Encryption & credentials > Install a certificate.
-
Select CA certificate.
-
Select Install anyway.
-
Verify your identity.
-
Choose the certificate file you want to install.
The root certificate is now installed and ready to be used.
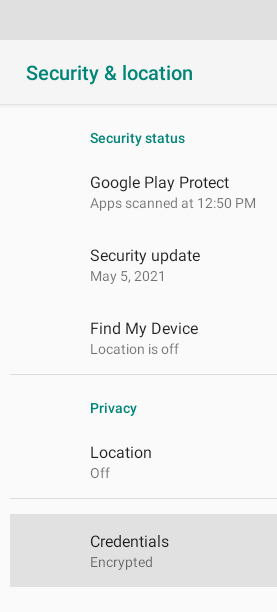
ChromeOS
-
Go to your ChromeOS Settings.
- Go to Apps > Google Play Store.
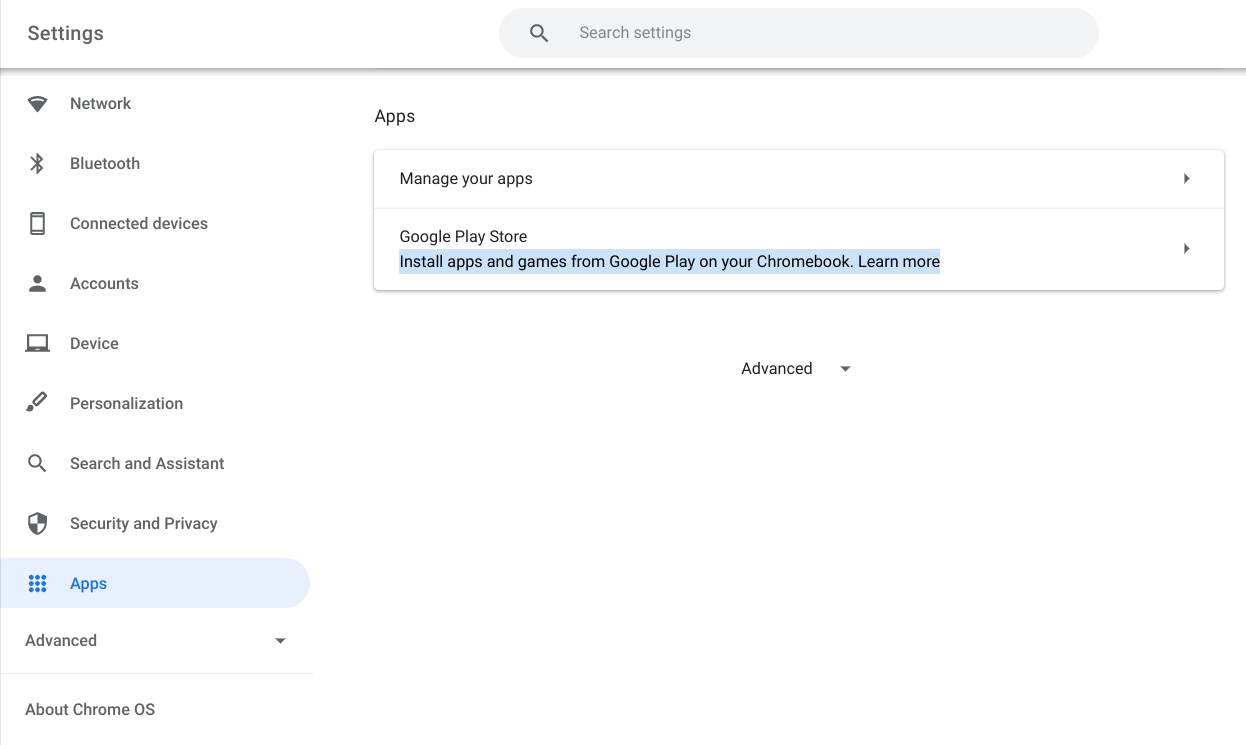
- Select Manage Android preferences.
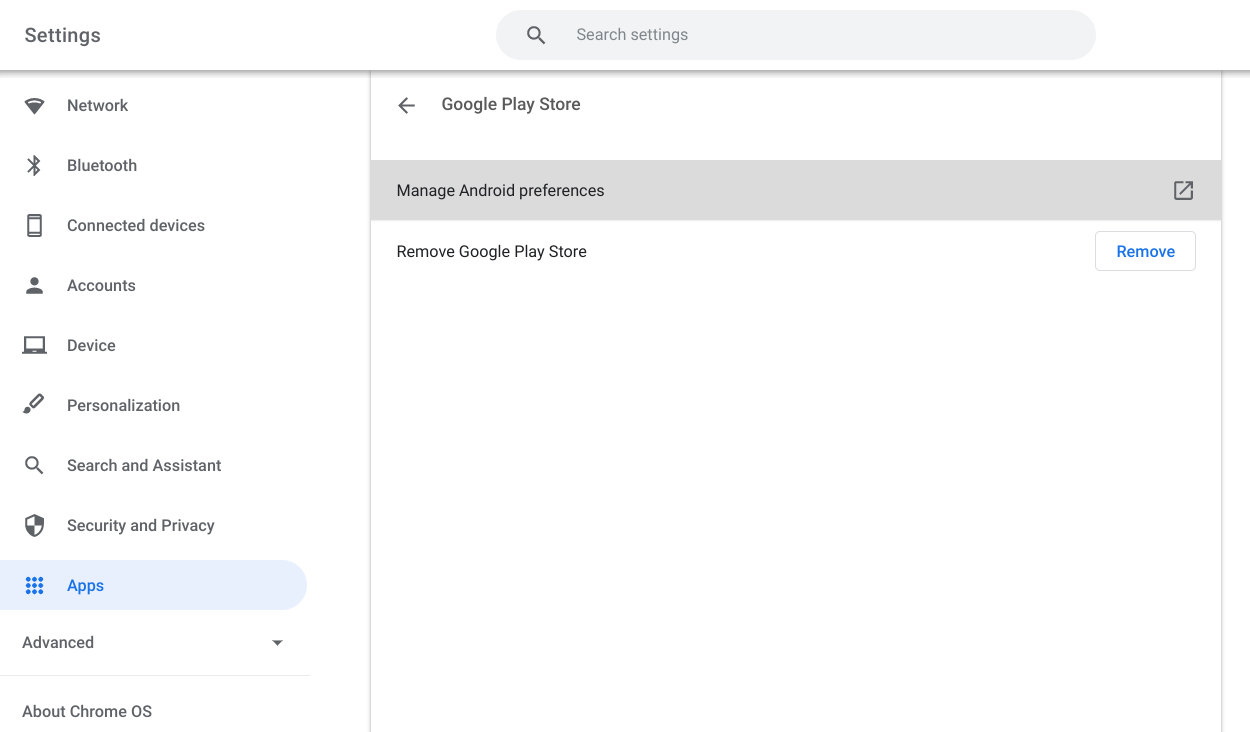
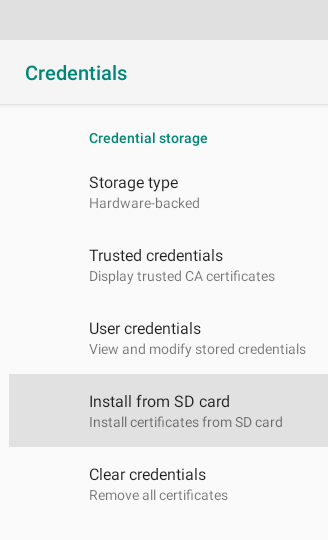
- Go to Security & location > Credentials > Install from SD card.
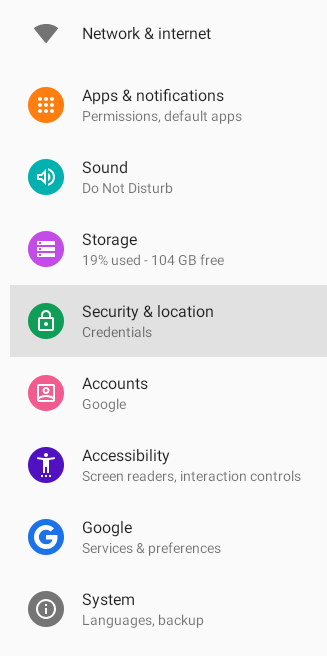
|
|
|
- In the file open dialog, select the
Cloudflare_CA.crtfile downloaded in step #1 and select Open.
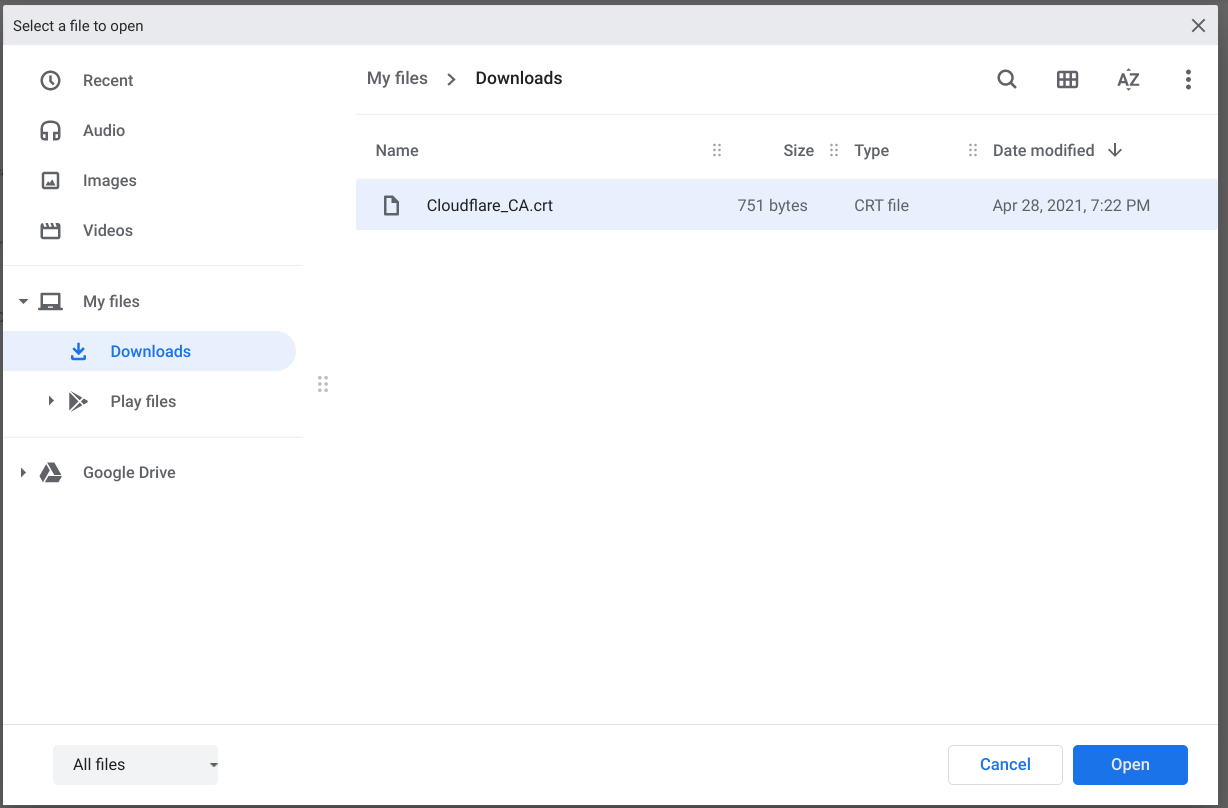
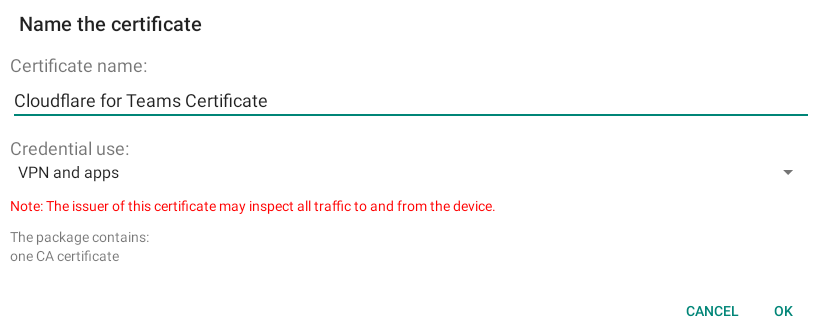
- Enter anything you want for the certificate name and select OK.
Add the certificate to applications
Some packages, development tools, and other applications provide options to trust root certificates that will allow for the traffic inspection features of Gateway to work without breaking the application.
All of the applications below first require downloading the Cloudflare certificate with the instructions above. On Mac, the default path is /Library/Keychains/System.keychain Cloudflare_CA.crt. On Windows, the default path is \Cert:\CurrentUser\Root.
Firefox
If your organization is using Firefox, the browser may need additional configuration to recognize the Cloudflare certificate. There are several ways you can add your Cloudflare certificate to Firefox. For more detailed instructions, see this Mozilla support article.
Python
Python on Windows
The command to install the certificate with Python on Windows automatically includes PIP and Certifi (the default certificate bundle for certificate validation).
-
Download the Cloudflare root certificate:
curl -o Cloudflare_CA.crt https://developers.cloudflare.com/cloudflare-one/static/documentation/connections/Cloudflare_CA.crt -
To update the bundle to include the Cloudflare certificate, run the following command:
gc .\Cloudflare_CA.crt | ac C:\Python37\Lib\site-packages\pip\_vendor\certifi\cacert.pem
Python on Mac and Linux
-
Install the
certifipackage:$ pip install certifi -
Identify the CA store:
$ python -m certifi~/Library/Python/3.7/lib/python/site-packages/certifi/cert.pem -
Download the Cloudflare root certificate:
$ wget https://developers.cloudflare.com/cloudflare-one/static/documentation/connections/Cloudflare_CA.pem -
Append the Cloudflare certificate to this CA Store by running:
$ echo | cat - Cloudflare_CA.pem >> $(python -m certifi) -
If needed, configure system variables to point to this CA Store:
$ export CERT_PATH=$(python -m certifi)$ export SSL_CERT_FILE=${CERT_PATH}$ export REQUESTS_CA_BUNDLE=${CERT_PATH}
Git
Git on Windows
-
Open PowerShell.
-
Run the following command:
This command will output:
core.symlinks=false
core.autocrlf=true
core.fscache=true
color.diff=auto
color.status=auto
color.branch=auto
color.interactive=true
help.format=html
rebase.autosquash=true
http.sslcainfo=C:/Program Files/Git/mingw64/ssl/certs/ca-bundle.crt
http.sslbackend=openssl
diff.astextplain.textconv=astextplain
filter.lfs.clean=git-lfs clean -- %f
filter.lfs.smudge=git-lfs smudge -- %f
filter.lfs.process=git-lfs filter-process
filter.lfs.required=true
credential.helper=manager
- The
http.sslcainfodefines the CA Certificate store. To append the Cloudflare certificate to the CA bundle, updatehttp.sslcainfo.
Git on Mac and Linux
Configure Git to trust the Cloudflare certificate.
npm
The command below will set the cafile configuration to use the Cloudflare certificate. Make sure to use the certificate in the .pem file type.
On some systems you may need to set the following in your path/export list:
Google Cloud SDK
The commands below will set the Google Cloud SDK to use the Cloudflare certificate. More information on configuring the Google Cloud SDK is available here.
-
Get curl’s
cacertbundle.$ curl -O https://curl.se/ca/cacert.pem -
Get the Cloudflare CA.
$ curl -O https://developers.cloudflare.com/cloudflare-one/static/documentation/connections/Cloudflare_CA.pem -
Combine the certs into a single
.pemfile.$ cat cacert.pem Cloudflare_CA.pem > ~/ca.pem -
Configure Google Cloud to use the combined
.pem.$ gcloud config set core/custom_ca_certs_file ~/ca.pem
Google Cloud SDK and Kaniko
Per the
gcloud documentation, if Kaniko is being used the Cloudflare certificate will need to be installed in the Kaniko CA store. Instructions can be found
here.
Google Drive for desktop
To trust the Cloudflare root certificate in the Google Drive desktop application, follow the procedure for your operating system. These steps require you to download the .pem certificate.
macOS
-
In the Finder menu bar, go to Go > Go to Folder. Enter
/Applications/Google Drive.app/Contents/Resources. -
Find
roots.pemand copy it to a permanent location, such as your Documents folder. -
Append the contents of
cloudflare.pemto the end ofroots.pem.$ cat ~/Downloads/Cloudflare_CA.pem >> path/to/roots.pem -
Apply the newly created root certificate to your Google Drive application.
$ sudo defaults write /Library/Preferences/com.google.drivefs.settings TrustedRootsCertsFile -string "path/to/root.pem"
You can verify the update with the following command.
Windows
-
In File Explorer, go to
\Program Files\Google\Drive File Stream\<version>\config\. -
Find
roots.pemand copy it to a permanent location, such as your Documents folder. -
Append the contents of
cloudflare.pemto the end ofroots.pem.$ cat ~\Downloads\Cloudflare_CA.pem >> path\to\roots.pem -
Update the Google Drive registry key.
$ reg ADD "HKEY_LOCAL_MACHINE\Software\Google\DriveFS" /v TrustedRootCertsFile /t REG_SZ /d "path\to\roots.pem"
You can verify the update with the following command.
For more information, refer to the
Google documentation for the TrustedRootCertsFile setting.
AWS CLI
If you’re using the AWS CLI, you need to set the AWS_CA_BUNDLE environment variable to use the Cloudflare root certificate. Commands are available for different operating systems in the instructions available
here.
PHP Composer
The command below will set the
cafile configuration inside of composer.json to use the Cloudflare root certificate. Make sure to use the certificate in the .pem file type.
Alternatively, you can add this manually to your composer.json file under the config key.
JetBrains
To install the Cloudflare root certificate on JetBrains products, refer to the links below:
Minikube
Instructions on how to install the Cloudflare root certificate are available here